Access Control Policy Tool
Access control mechanisms control which users or processes have access to which resources in a system. Access control policies are increasingly specified to facilitate managing and maintaining access control. However, the correct specification of access control policies is a very challenging problem. This problem becomes increasingly severe as a system becomes more and more complex, and is deployed to manage a large amount of sensitive or private information and resources.
To provide high security confidence levels for the nation’s critical IT infrastructure, it is important to provide a tool, which can thoroughly and automatically check the syntactic and semantic faults of AC policies before deploying them for operation. NIST’s effort of developing the tool – Access Control Policy Tool (ACPT) – provides:
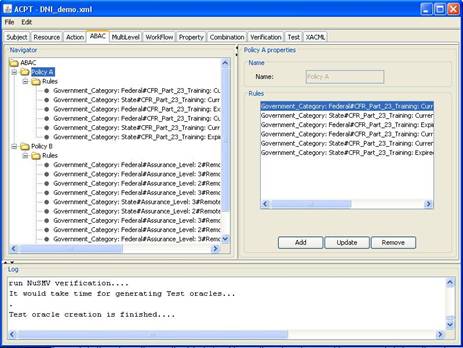
- GUI templates for composing AC policies,
- property checking for AC policy models through an SMV (Symbolic Model Verification) model checker,
- complete test suite generated by NIST’s combinatorial testing tool ACTS, and
- XACML policy generation as output of verified model.
Through the four major functions, ACPT performs all the syntactic and semantic verifications as well as the interface for composing and combining AC rules for AC policies; ACPT assures the efficiency of specified AC policies, and eliminates the possibility of making faulty AC policies that leak the privacy information or prohibit legitimate information sharing. NIST has developed this tool, because so far, there is no project or research similar to the ACPT. NIST has significant experience and has great success in developing and transferring access control technologies. In regard to cyber security, privacy, and information sharing, access control is one of the crucial elements in protecting the nation’s critical IT infrastructures for healthcare, transportation, financial, power grids, military, intelligence, and safety systems, etc. It is essential to have measurement technology such as ACPT for access control policy administrators and authors to ensure the safety and flexibility in composing and combining their access control policies. Thus, the developing of ACPT meets the mission of the Computer Security Division, according to the Federal Information Security Management Act of 2002 (FISMA). Introduction of ACPT slides can be downloaded in the Reference Section below.
ACPT is currently available as a prototype system; it contains model templates for three major access control policies: static Attribute-Based access control, Multi-Leveled Security, and stated Work-Flow. New and improved features will be added for the future versions. To learn more about ACPT please review these presentation slides. NIST welcomes joint effort in developing ACPT, please contact the project lead listed in the Contacts for further information.
Our research includes:
- Access control policy composition and combination
- Access control model and property verification
- Automation of access control policy generation
- Test suite generation for access control implementation.
Cooperation:
- Prof. Tao Xie, Computer Science Department of University of Illinois at Urbana-Champaign.
- Prof. Jai Di, Prof. Qinghua Li, Ang Li, Wei Bao Department of Computer Science and Computer Engineering of University of Arkansas
- JeeHyun Hwang, Computer Science Department of North Carolina State University.
- Nathan Jacobson, Computer Science Department of Hood College
- Bruce Batson, Computer Science Department of Virginia State University
Beta Release:
The Access Control Policy Tool (ACPT) is developed by NIST Computer Security Division and North Carolina State University, and is sponsored by the Director of National Intelligence. Click here to learn how to obtain the Beta Release tool.
References:
- V. C. Hu, D. R. Kuhn, & Y. Dylan NIST SP 800-192, Verification and Test Methods for Access Control Policies/Models, June, 2017.
- A. Gouglidis, I. Mavridis, & V. C. Hu, Security policy verification for multi-domains in cloud systems, Int’l Journal of Information Security (IJIS13), article No. 13(2), 97-111, July, 2014.
- A. Gouglidis, I. Mavridis, & V. C. Hu, Verification of Secure Inter-operation Properties in Multi-domain RBAC Systems, IEEE Seventh International Conference on Software Security and Reliability (SERE 2013), Washington, D.C., USA, June, 2013.
- V. Hu, Access Control Policy Tool, Introduction of Access Control Policy Tool in Power Point slides.
- V. Hu, D.R. Kuhn, T. Xie, J. Hwang, Model Checking for Verification of Mandatory Access Control Models and Properties, Int'l Journal of Software Engineering and Knowledge Engineering (published in IJSEKE journal, Vol. 21, No. 01, February 2011).
- V. Hu, D.R. Kuhn, T. Xie, Property Verification for Generic Access Control Models, IEEE/IFIP International Symposium on Trust, Security, and Privacy for Pervasive Applications, Shanghai, China, Dec. 17-20, 2008.
- J. Hwang, T. Xie, V. Hu, Detection of Multiple-Duty-Related Security Leakage in Access Control Policies,The Third IEEE international conference on Secure Software Integration and reliability improvement (SSIRI), Beijing China, July 8-10, 2009.
- E. Martin, J. Hwang , T. Xie , and V. Hu, Assessing Quality of Policy Properties in Verification of Access Control Policies, Annual Computer Security Applications Conference (ACSAC), December, 2008.Anaheim, California.
- V. Hu, E. Martin, T. Xie, Conformance Checking of Access Control Policies Specified in XACML, Proceedings, The First IEEE International Workshop on Security in Software Engineering (IWWSE), Beijing China, July 23-27, 2007.
- NIST/NSA Privilege (Access) Management Workshop (2009).
- Testing and Analysis of Security Policies Web site from Computer Science Department of North Carolina State University.









DISCLAIMER :
Certain software products are identified in this document. Such identification does not imply recommendation by NIST, nor does it imply that the products identified are necessarily the best available for the purpose.